ISMS Dashboard
These are all risks for the security of information in companies. Numerous laws (e.g. IT Security Act, EU GDPR), regulations and industry-specific rules and standards (e.g. B3S, IT security catalog) therefore require systems and rules to ensure information security in a company in the long term. Information is now so important that protecting it is a top priority and must be ensured responsibly and continuously.
A professional information security management system (ISMS) is crucial in order to successfully meet the requirements and challenges of information security in the company and to maintain the protection goals. ISMS software establishes procedures and rules for the permanent management, control, maintenance and continuous improvement of information security. An ISMS is designed in accordance with ISO standards such as ISO 27001 or the specifications of the BSI. Without the support of software-supported ISMS solutions, successful and long-term operation in accordance with regulatory requirements is not possible in the long term.
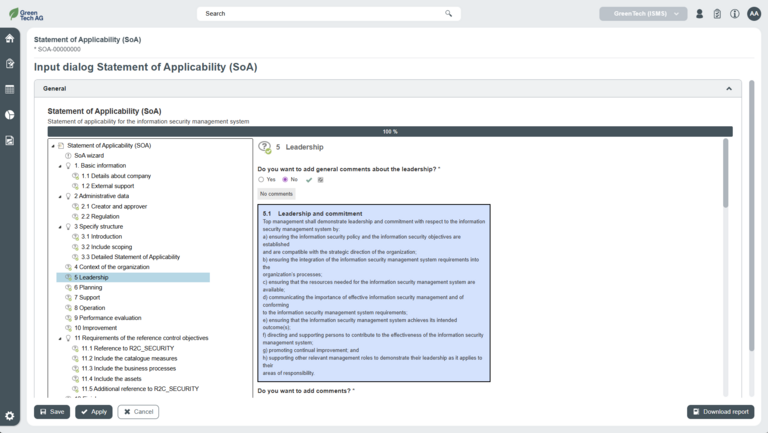
Schleupen GRC's ISMS software provides you with an efficient, open-standard tool for managing your ISMS processes that is tailored to your information security concepts. With our information management system, you can initiate, implement and monitor procedures and measures for information security and carry out continuous checks and improvements. R2C_SECURITY supports you in all phases of the process, from the selection of the relevant standards to the certification-ready organization.
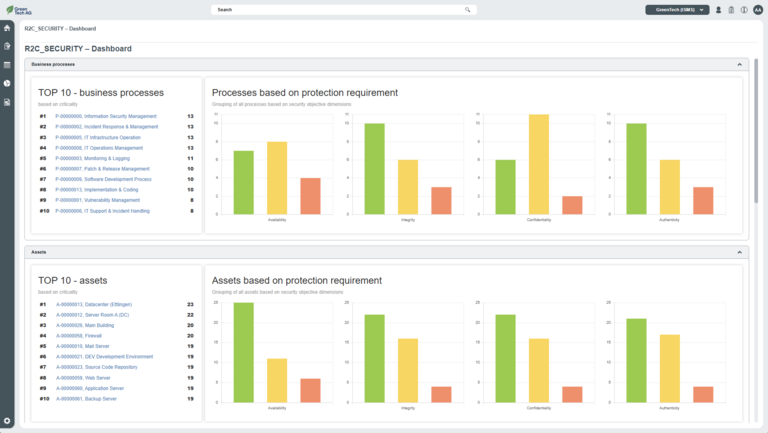
Reporting is rarely the issue itself. The effort behind it usually is. Collecting data, processing it, and presenting it in a clear and meaningful way often takes a considerable amount of time. Our Insights reporting and dashboard features significantly reduce this effort. With just a few clicks, you can generate real-time reports. Information is provided in a structured and automated way, eliminating the need for time‑consuming manual processing. A centralized overview of statuses, trends, and action items, directly within your system, ensures that insights are available exactly where decisions are made.
The importance of an ISMS in the context of NIS2
An information security management system (ISMS) is an important tool for companies and organisations to meet the requirements of the NIS2 directive. The introduction of an ISMS provides companies with a structured approach to managing information security that helps them to identify their organisation's critical business processes and IT systems, analyse the risks associated with cyber threats, implement appropriate state-of-the-art measures and continuously monitor the security situation in order to detect security incidents at an early stage and respond appropriately.
Two of the leading standards for information security management systems (ISMS) in Germany are ISO 27001 and the BSI IT baseline protection compendium. Both standards provide a recognised framework for setting up, implementing, operating and maintaining an information security management system (ISMS).
For the effective implementation and management of an ISMS, R2C_SECURITY offers you a flexible and open-standard software solution (e.g. ISO 27001, BSI IT baseline protection, B3S, IT security catalogue and many more) with comprehensive functions for setting up, operating and maintaining an ISMS. With R2C_SECURITY, organisations can efficiently manage their information security processes and ensure compliance with recognised norms and standards.
Implementation in Germany and what you need to know about NIS-2-UmsuCG
In the age of digital attacks and advanced cyber threats, the NIS2 Directive is an EU response to increase the resilience of member states to cyber attacks.
The NIS2 Directive sets out requirements that companies and organisations, in particular operators of essential services (OES) and digital service providers (DSPs), must comply with. The requirements include measures to prevent cyber attacks, detect security incidents and respond to these incidents in order to ensure the continuous availability of critical services.
The NIS2 directive ensures that companies and organisations implement appropriate state-of-the-art security measures to protect their systems and critical services from cyber threats.
What is the NIS-2 Directive? |
|
When does the NIS 2 Directive apply? |
|
What is the NIS2UmsuCG? |
|
Who is affected by the NIS2UmsuCG? |
|
The companies and organisations in Germany affected by the NIS2 Implementation Act consist of four groups:
- Operators of critical facilities (KRITIS facilities)
- Operators of particularly important facilities
- Operators of important facilities
- Operators of federal facilities
When the NIS 2 Implementation Act comes into force, there will be two groups of sectors in future:
- KRITIS sectors
- Sectors for important facilities (defined in Annex 1 & 2 NIS-2-UmsuCG)
Operators of critical facilities (KRITIS facilities):
- The previous KRITIS operators, the critical infrastructures, will become operators of critical facilities. At the same time, the operators become particularly important facilities
- The KRITIS logic of KRITIS sectors, critical services and KRITIS facilities with threshold values (usually ≥ 500 thousand households supplied) is retained here
Particularly important facilities
- Large companies in the facilities sectors and some companies regardless of their size:
- Companies with 250 or more employees or
- Companies with a turnover of EUR 50 million or more and a balance sheet of EUR 43 million or more or
- Special cases: qTSP, TLD, DNS, telecommunications providers, critical facilities, central government
- KRITIS system operators
Important facilities
- Medium-sized companies in the facilities sectors
- Companies with 50 or more employees or
- Companies with a turnover of EUR 10 million or more and a balance sheet of EUR 10 million or more or
- Trust services.
The NIS 2 Implementation Act provides for various deadlines for the implementation of the requirements, with the NIS2UmsuCG Act itself expected to come into force in October 2024.
For the affected groups, registration in accordance with §33 (1) and (2) must take place within three months of the NIS2UmsuCG coming into force.
For operators of critical facilities, the first proof of the implementation of measures must be provided no later than a date specified by the BSI (Federal Office for Information Security) and BBK (Federal Office of Civil Protection and Disaster Assistance) upon registration, which is no earlier than three years after the Act comes into force in accordance with Section 39 (1) - i.e. from 2027.
For particularly important organisations, the law stipulates that participation in the exchange of information must take place within one year of the NIS2UmsuCG coming into force in accordance with Section 30 (7).
The registration obligation applies to important institutions.
- R2C_SECURITY is a multi-client capable system.
- The organizational structure can be mapped via the client hierarchy in order to map the scope of the ISMS for the organizational structure
- The multi-client capability means that any level of organizational structure can be mapped
- The ISMS software from Schleupen is an open standard system
- The ISMS software enables you to work in accordance with the requirements of national and international
- norms and standards, e.g. BSI IT baseline protection compendium, ISO 27001, 27002, 27005, 27019, 27701, B3S, BAIT, VAIT, TGK, NIST
- Other standards, industry requirements, legal requirements, internal guidelines and company standards can be easily integrated and managed
- The scope of application, i.e. which standards, specifications and guidelines apply to the ISMS, can be defined individually for the clients
- Management of business processes and assets of any type, e.g. information, applications, IT systems, infrastructure, buildings, rooms, personnel
- Mapping of business process and asset hierarchies in any depth
- Designation of responsibilities, maintenance of descriptions and other detailed information as well as the option to define optional mandatory fields
- Analysis of the impact of damage for individual business processes and assets on the basis of freely configurable damage scenarios
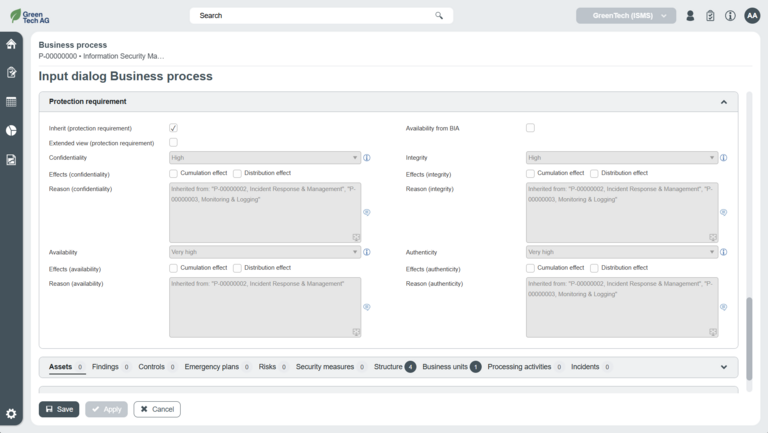
- Implementation of protection requirement analyses for the protection objectives of confidentiality, integrity, availability and authenticity, including assets/business processes and automatic inheritance of protection requirements with configurable inheritance direction
- Consideration of dependencies such as accumulation and distribution effects
- Further protection objectives and assessment dimensions can be freely defined in the ISMS software and optionally activated
- Implementation of business impact analyses (BIA)
- Dashboards, reports and evaluations for monitoring business and time-critical business processes and assets
- Upload documents via drag & drop
- Interfaces for data import & export (manual, time-controlled and automatic)
- Flexible expandability of the ISMS software with customer-specific features (customizing)
- Recording and documentation of information security risks and classification into freely configurable risk categories
- Designation of responsibilities using ISMS software
- Integration of individual threat and vulnerability catalogs to carry out detailed risk analyses
- risk analyses
- Implementation of protection target-related risk analyses with automatically inherited impact
- Extended risk assessment based on individual threat catalogs
- Individual consideration of risks before and after the implementation of risk-reducing protective measures (gross/net consideration)
- Definition of risk treatment strategies (e.g. reduction, avoidance)
- Submission of declarations on the acceptance of residual risks
- Dashboards, reports and evaluations for monitoring the risk situation
- Drag & drop for uploading documents
- Straightforward data import & export (manual, time-controlled and automatic)
- Flexible expandability with customer-specific properties (customizing)
- Recording and comprehensive documentation of protective measures, from planning and implementation to appropriateness and effectiveness testing as well as cost recording and scheduling
- Designation of responsibilities
- Linking of protective measures with requirements/controls from standards, legal requirements, internal guidelines and company standards as a basis for GAP analyses and audits
- Sending email notifications to remind you when measures are due
- Dashboards, reports and evaluations to monitor the degree of compliance
- Upload documents via drag & drop
- Interfaces for data import & export (manual, time-controlled and automatic)
- Flexible expandability with customer-specific properties (customizing)
- Quick recording and comprehensive documentation of information security incidents in the ISMS software
- Appointment of incident handlers
- Assignment of affected business processes and assets as well as risks that have occurred
- Classification of the impact on the protection goals of confidentiality, integrity, availability and authenticity as well as assessment of criticality and damage incurred
- Definition of protection and improvement measures
An audit is a quality management tool that examines whether the defined protection objectives have been achieved, the relevant security requirements are met and the company's critical assets are adequately protected. Internal and external audits as well as self-audits can be carried out in Schleupen's ISMS software. Which norms and standards, which sub-areas thereof or which business processes are to be audited can be decided according to the situation.
In addition to the comprehensive options within an audit, our ISMS software can define audit procedures for each audit checkpoint and document random samples and results. In the event of deviations, findings are created, comprehensively described and assigned to a responsible person. Standard evaluations and reports present the audit results in a reliable, transparent and comprehensible manner.
Our ISMS software offers effective management of your information security and is still very user-friendly and intuitively understandable. Benefit now from the numerous advantages of Schleupen's ISMS software:
- Comprehensive lists and detailed views - Users can customize the columns displayed in a list and their order. In addition, lists have extensive sorting and filtering options that can be saved user-specifically.
- Simple list export to EXCEL and CSV files - All lists can be exported as Excel or CSV files.
- Full-text search - The integrated search function enables a full-text search for all transaction data created in the application and displays the search results in the legal context of the logged-in user.
- Journal entries and change comments - All changes made to the element called up, e.g. to an asset, are automatically journalized. In addition, change comments can be entered in read-only mode. Changes, decisions and resolutions thus remain traceable even years later.
- Atlases - Atlases contain a hierarchical representation (tree structure) of all elements that have been linked to each other. Atlases can be freely configured and created on a client-specific or cross-client basis.
- My portfolio - the "My portfolio" overview page provides an overview of