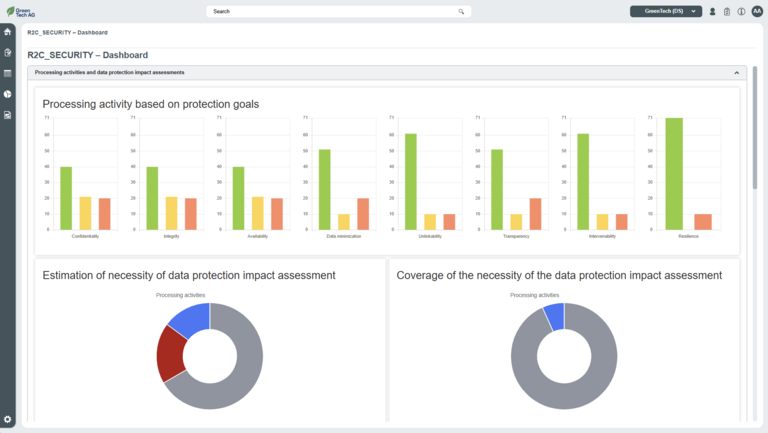
Dashboard data protection
What requirements must good data protection management software meet? In order to properly protect personal data, data protection management software must comply with the EU GDPR guidelines. Since May 25, 2018, companies have the following obligations under the new General Data Protection Regulation, among others
- Knowledge of the collection and processing of personal data.
- Proven compliance with data protection regulations.
- Notification of data breaches within three days.
- Prompt response to requests for information.
- Immediate secure deletion of superfluous or unlawful personal data.
- Possibility of appointing a data protection officer in certain cases.
The EU GDPR (Chapter IV) requires the creation of a record of processing activities (Art. 30 EU GDPR) and data protection impact assessments (Art. 35 EU GDPR) in the event of a high risk. In addition, suitable technical and organizational measures must be taken to ensure data security.
Data and information protection are continuous tasks. Schleupen GRC's data protection management software offers professional, transparent and GDPR-compliant implementation and maintenance of this process, developed by experts to reliably secure all personal data in your company.
- Integrated management system for information security and data protection that supports relevant certifications
- Short implementation time due to high level of standardization
- High acceptance of the software thanks to simple and modern operating concept
- Documentation of data protection in accordance with the EU GDPR
- Audit-proof data storage and historization
- Customer support with in-house employees
- Software made in Germany
- Analysis of protection requirements from a data protection perspective
- Recording and controlling all measures to ensure data security and lawful data processing
- Recording, reporting and handling of data protection incidents
- Monitoring all processes, assets, risks and measures using meaningful dashboards and reports
- Conducting internal audits and self-audits to ensure and maintain data protection, e.g. in accordance with ISO 27701
Reporting is rarely the issue itself. The effort behind it usually is. Collecting data, processing it, and presenting it in a clear and meaningful way often takes a considerable amount of time. Our Insights reporting and dashboard features significantly reduce this effort. With just a few clicks, you can generate real-time reports. Information is provided in a structured and automated way, eliminating the need for time‑consuming manual processing. A centralized overview of statuses, trends, and action items, directly within your system, ensures that insights are available exactly where decisions are made.
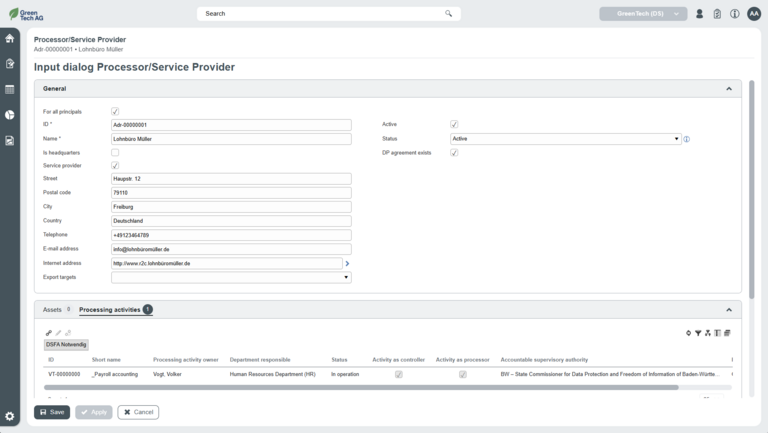
The data protection solution is designed so that companies can access the basic elements of business process, asset, risk and measure from ISMS clients and link them to the documented processing activities in the data protection client.
Advantage: The shared database for information security and data protection enables the simple use of data that has already been created, such as business processes, assets (e.g. information, applications, infrastructure, personnel), risks and measures. No redundant data needs to be maintained.
However, business processes, assets, risks, protective measures and other fundamental elements can of course also be documented independently for data protection.
The record of processing activities is a central component of the EU GDPR. For this purpose, essential information must be provided on:the purposes of data processing, the categories of data subjects, personal data and recipients, as well as the planned deadlines for deleting the various categories of data.
- The data protection management system offers companies and data protection officers the opportunity to record all aspects relevant to data protection in a structured and convenient manner.
- The input mask for the processing activities can be flexibly expanded to include customer-specific properties (customizing).
- Collecting and carrying out risk assessments from a data protection perspective (integration of data protection criteria into the assessment)
- Integration of individual threat and vulnerability catalogs to carry out detailed risk analyses
- Definition of risk treatment strategies (e.g. reduction, avoidance)
- Definition of technical and organizational measures (TOMs)
- Establishing links to data protection impact assessments, processing activities, data protection incidents, procedures (business processes), assetsx
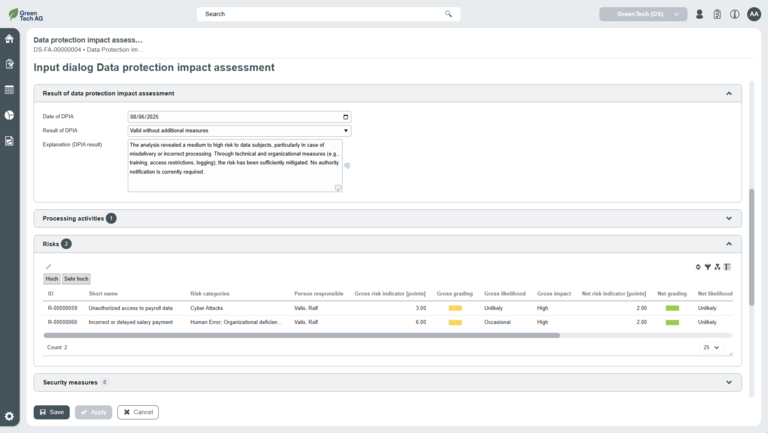
A data protection impact assessment is the assessment of the consequences of processing operations for the protection of personal data if the form of data processing is likely to result in a high risk to the rights and freedoms of natural persons (see Art. 35 para. 1 GDPR).
- Our solution supports you in deciding whether it is necessary to carry out a data protection impact assessment. This can be created for one or more processing activities.
- The input mask for the data protection impact assessment can be flexibly extended to include customer-specific properties (customizing).
- Register of processing activities
The "Record of processing activities" report provides all the information required by the EU GDPR at the touch of a button and can be made available to the supervisory authority on request. The register can be created both from the perspective of a controller and from the perspective of a processor.
- Data protection impact assessment
The "Data protection impact assessment" report provides all the information required by the EU GDPR at the touch of a button and can be used, for example, as part of a consultation with the supervisory authority.